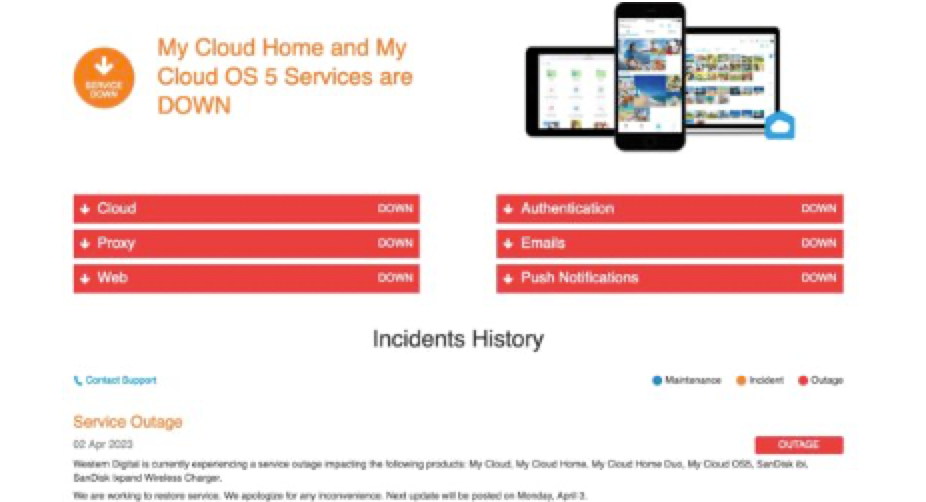
Western Digital fell victim to a cyberattack on March 26th, after hackers were able to breach their internal networks. Investigative reports indicate that company data was stolen. In response, the company shut down cloud services for two weeks as well as mobile, desktop, and web apps for customers.
“[The incident] has caused and may continue to cause disruption to parts of the [company’s] business operations.”
Hacking group, ALPHV – also known as BlackCat – claimed responsibility for the hack, and demanded that Western Digital negotiate a ransom payment to them to prevent insider data from being leaked.
Dominic Alvieri, a security researcher for Western Digital, reported that ALPHV released “twenty-nine screenshots of emails, video conferences, and documents related to the company’s response to the attack”. This means that even as Western Digital attempted to deal with the breach, the hackers were still inside of their systems and able to see what the company was trying to do.
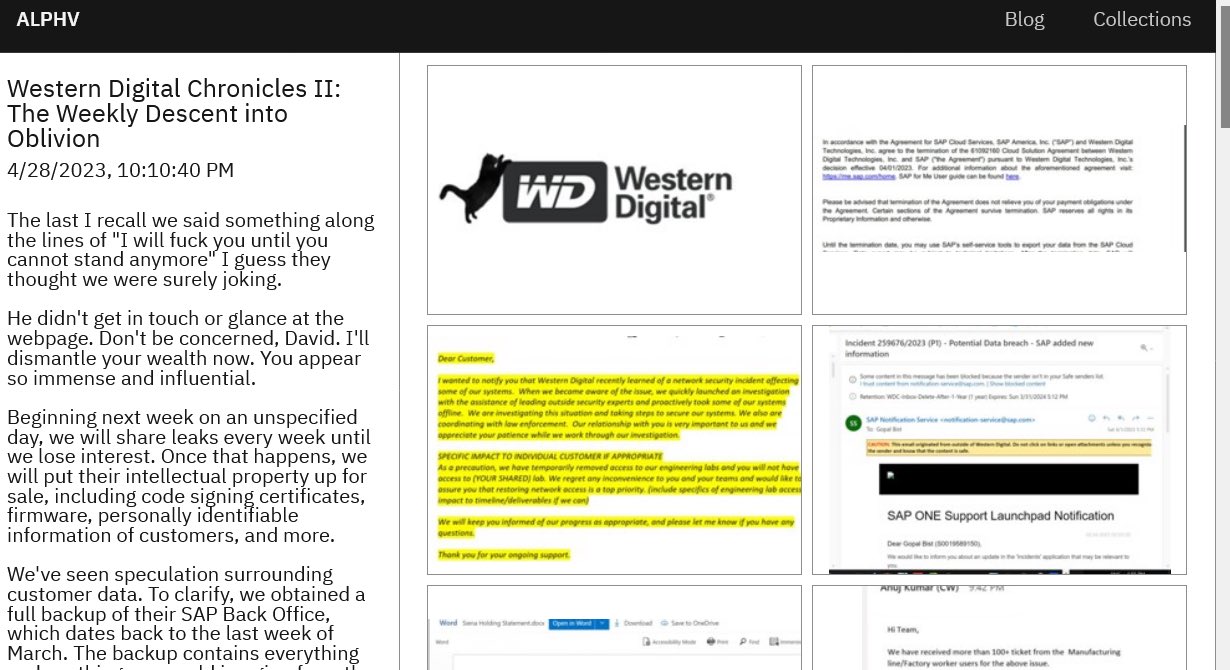
ALPHV also states that they have customers’ personal information as well as a backup of the SAP Backoffice implementation of the company, amounting to around 10 terabytes of data. The group has allegedly announced a ransomware payment to Western Digital who have not yet disclosed the amount. Cybersecurity experts estimate the amount to be a minimum of 8 figures.
Western Digital’s lack of public reports and transparency over the breach has been less than stellar for customers, who were unable to access any services for their storage devices for days. Shares of WD have fallen over 4.5%. Online services have since been restored; however, customers are still in the dark about the scope of the breach as Western Digital continues to investigate.
With over 25 years of experience, we at Motiva Networks can help you plan and see if your data has been compromised with a Free Confidential Cybersecurity Risk Assessment. Or you can schedule a quick 10-minute call to discuss the best options for your Agency or small business, or go over any questions you might have HERE.